Catching the ghost: how to discover ephemeral evidence with Live RAM analysis
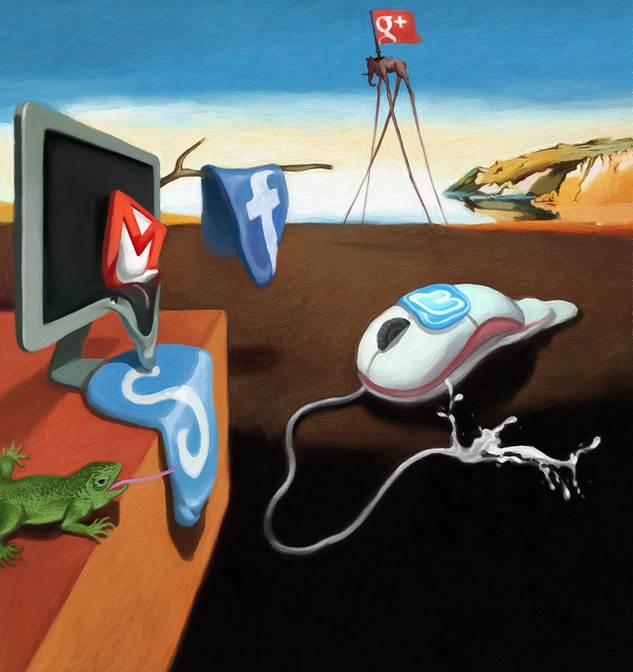
Belkador Dali. “Losing volatile Evidence”.
All rights reserved.
Published in DFI Magazine, May 2013
Contents
- Ephemeral Evidence
- The Role of Live RAM Analysis in Today’s Digital Forensics
- Types of Evidence Available in Volatile Memory
- Limitations of Volatile Memory Analysis
- Collecting Volatile Data that Can Withstand Legal Scrutiny
- Acquisition Footprint
- Live Box vs. Offline Analysis
- Standard Procedure
- Tools and Techniques for Capturing Memory Dumps
- Consequences of Choosing the Wrong Tool
- The FireWire Attack
- The “Freezer Attack” on Scrambled Smartphones
- Tools for Analyzing Memory Dumps
- About the Authors
- Contacting the Authors
- About Belkasoft Research
- About Belkasoft
- References
Ephemeral Evidence

Until very recently, it was a standard practice for European law enforcement agencies to approach running computers with a “pull-the-plug” attitude without recognizing the amount of evidence lost with the content of the computer’s volatile memory. While certain information never ends up on the hard drive, such as ongoing communications in social networks, data on running processes or open network connections, some other information may be stored securely on an encrypted volume. By simply pulling the plug, forensic specialists will slam the door to the very possibility of recovering these and many other types of evidence.
The Role of Live RAM Analysis in Today’s Digital Forensics
Capturing and analyzing volatile data is essential for discovering important evidence. Making a RAM dump should become a standard operating procedure when acquiring digital evidence before pulling the plug and taking the hard drive out.
